I’m traveling soon. Why not pair with a social fast? Then it hit me: everyone should social fast while traveling. I owe a huge thanks to artist and friend Gage Lindsten for reminding me social network fasts are a thing. Three reasons why you should social fast while traveling:
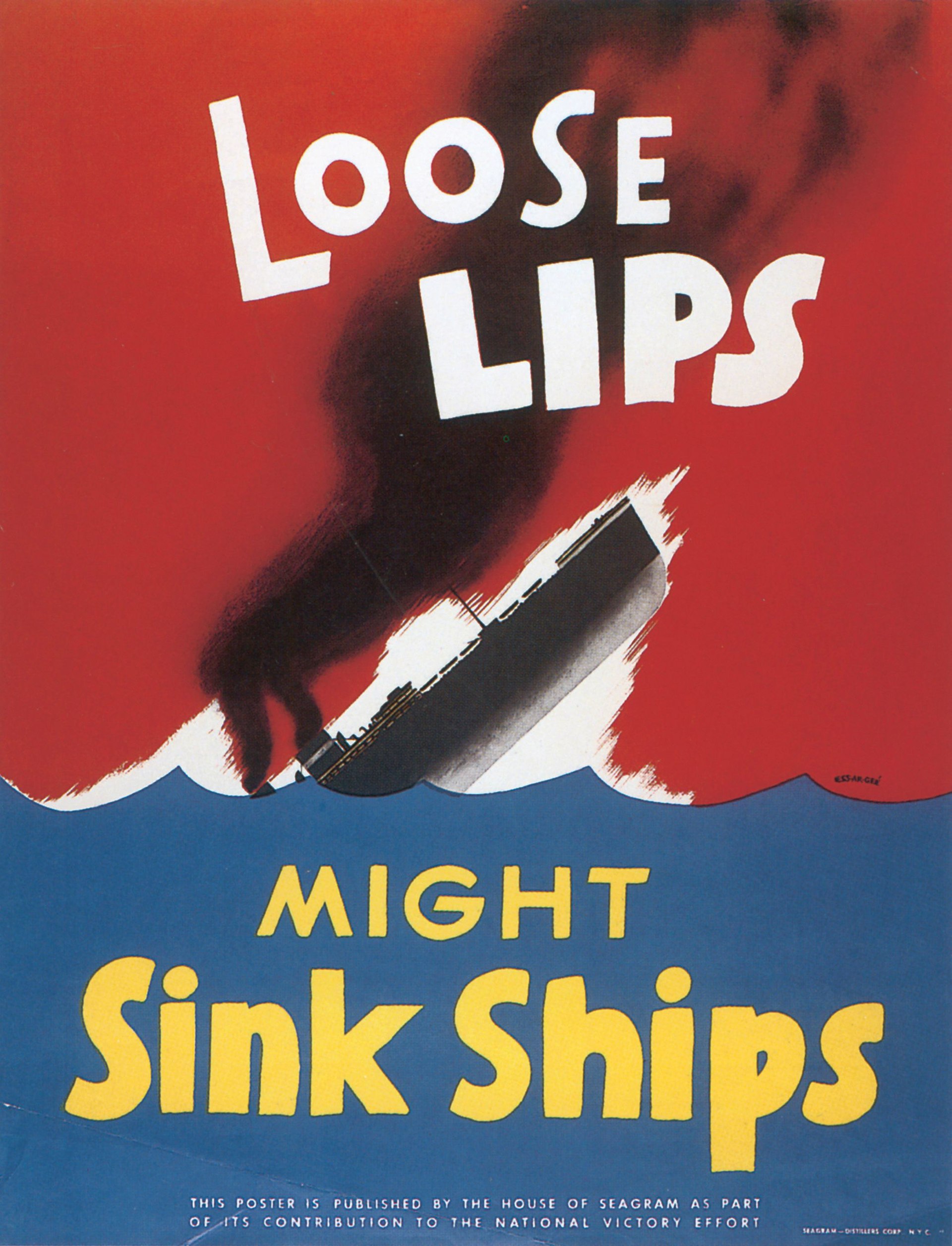
- We’re at war.
- Nothing is good enough.
- It is going to get more interesting before it gets less interesting.
Pop quiz! Are You In WWIII?
For almost a decade, I have considered myself an active participant in WWIII. In the last ten years:
- How many data breaches compromised your private and medical data?
- How many times was your data sold without your knowledge?
- How many tomes of EULA, T&C, Privacy Policy, and waivers have you scrawled your lo-res initials on?
- How many times was your information surgically targeted by bad actors?
- How many frauds were committed with some or all of your data?
- How many of your exasperated, “Oh, aren’t computers just frustrating sometimes?” moments were actually something more sinister?
The answer to all these questions - for everyone who has ever used a computer! - is the same: it is impossible to know.
And that is exactly my point. Because we are all active participants WWIII, some people just don’t realize it yet. And no degree of caution is good enough.
Nothing is Good Enough
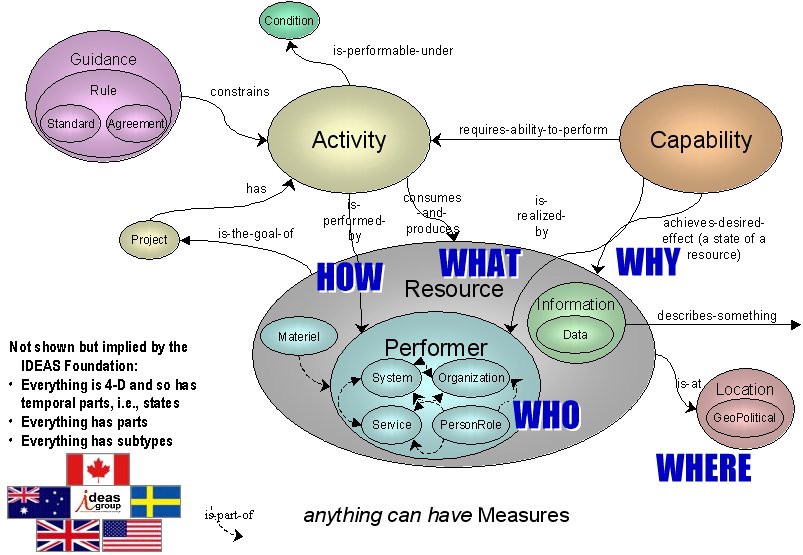
This wild infographic is allegedly owes provenance to the Department of Defense Architecture Framework.
I think of myself as a careful and technical fellow. I lean chaotic-good with most matters. But… a glimpse into my data-life:
- I use DuckDuckGo instead of Google.
- I use Brave instead of Safari.
- I use a password manager in all situations.
- I reserve the right to not use a password manager in certain situations.
- I don’t re-use passwords.
- I regularly cycle passwords.
- I use 2FA.
- I use biometrics.
- I use virtual private networks.
- I use pi-holes.
- I keep my applications patched and updated.
- I use encryption.
- I write software that uses encryption.
- I use backup codes.
- I have hardcopies of backup codes in firesafes at geographically separate locations.
All these measures are not good enough. My answer to, “Pop Quiz! Are You in WWIII?” is the same as yours. (All our answers are the same, remember.)
Why Social Fast While Traveling?
Imagine…
Day one of your vacation was full of adventures. You’re in the warm amber light dinner and friends. You excuse yourself. Your phone won’t unlock. Now it is resetting. Someone has engaged the remote wipe protocol.
“They’d need my watch to do that.”
You realize your smart-watch is missing; undoubtedly lost on that hike…
Imagine…
Instagramming a concert in a new city. You get a call from your landlord in the morning that your rental unit was broken into and all your belongings stolen. Later, you learn of a zero-day exploit in a popular IoT device.
“I didn’t even use that thing.”
Doesn’t matter if it’s connected to your wi-fi. They were just waiting for you to be gone for a few days.
Imagine…
You arrive at LAX after a domestic flight. You are detained. There was another outbreak. But you were not in that city, you protest. The official reveals a photo of you tagged in the vicinity.
“But I was on the highway, 70mph.”
You contract the new virus from other detainees.
I could write these little nightmares all day. I don’t believe these things are likely to happen to me. But I have the imagination to see how they could.
Things are not going to stop happening. Sharing what you’re doing while traveling in 2022 comes with a higher risk profile than I am willing to allow.
What About Security Through Obscurity?
“Security through obscurity,” is the philosophical notion that you are safest if you reveal as little information as possible. Secrecy is your primary armor. While appealing on the surface, this has been rejected by military and security professionals for decades. Many of them ascribe to the NIST recommendation:
“System security should not depend on the secrecy of the implementation or its components.”
Meaning it shouldn’t matter if you know I use a strong password and 2FA to access a particular website. The strong password and 2FA should be resilient enough on their own. (Tangent: this is one of the reasons why we get to worry about so called “quantum supremacy,” a situation in which a world power gains the capability to crack all existent security protocols with a new type of quantum computer.)
Musky Twitter
And this in a really round about way brings us to the current Musk / Twitter controversy. (For those of you reading in the far future, it looks like Musk is going to acquire Twitter for $44 billion.)
There is a future where Musk, personally, will be able to read your DMs. He’ll have jolly green terminal screen to clickity-clack your name into and pull up ever Twitter handle you’ve ever had. And read every message you ever sent. Every message his exes ever sent…
Free speech is pretty asymmetrical when you take unfathomable into the equation, eh?
In a world where your data can be sold to the highest bidder, the chain of custody is terminally compromised.
“But I Don’t Have Anything to Hide.”
Until precisely the instant something changes and we do.
Don’t let your travels be a leaky ship.
Go forth and adventure. Be present.
Share it when you get back.
